Vulnerability Management Home Lab


Nessus is one of many vulnerability scanners an organization can use to monitor their network, systems, and software applications for any potential security vulnerability.
Nessus works by running a test on each port on a target machine to determine the services running and any potential vulnerabilities related to them.
In this lab, we will be creating our target machine using VMWare Workstation and using Nessus Essentials to run three different vulnerability scans against our target machine:
- Uncredentialed scan
- No credentials will be provided to scan
- Credentialed scan
- Local admin credentials will be provided to scan
- Credentialed scan with deprecated application
- A deprecated version of Mozilla Firefox will be installed before credentialed scan
- Uncredentialed scan
- Install and configure Nessus and perform credentialed vulnerability scans against Windows 10 host
- Implement Vulnerability Management Function on sandbox network:
- Discover, Prioritize, Asses, Report, Remediate, Verify
- Conduct vulnerability assessments with Nessus; remediate vulnerabilities
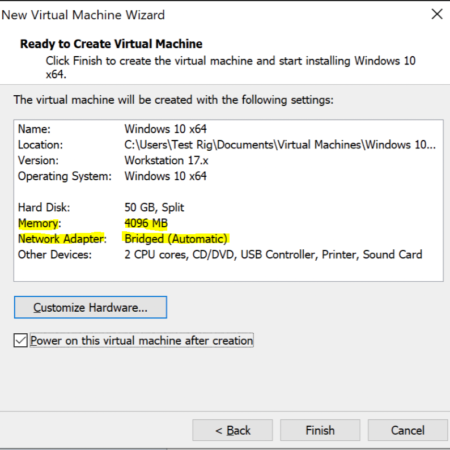
First we will be creating a virtual machine loaded with Windows 10 to serve as a machine that we will be running vulnerability scans against. Our VM will be hosted using VMWare Workstation. The windows 10 iso file can be downloaded here for free.
Regarding the hardware setup for our VM, we have increased the memory from 2GB to 4GB for increased performance and changed our network adapter from NAT to Bridged so that our VM is on the same network as our physical PC. This will allow Nessus to talk to our VM more easily.
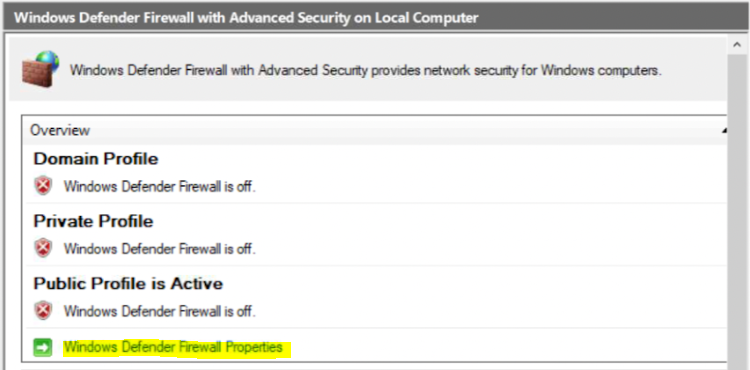
Once Windows 10 is set up, we will then turning off the Windows Firewall by turning off the firewall for the Domain, Private, and Public profile. This can be changed by typing “wf.msc” on the windows search and selecting “Windows Defender Firewall Properties”
Nessus Essentials is a open source vulnerability scanner that we will be using to scan our Windows 10 VMs. Nessus will raise any alert if it discovers any vulnerabilities that malicious hackers could use to attack our system.
Nessus Essentials is free for download here. Once Nessus Essentials is installed and registered, you will be directed to the web portal below to register your activation key and set up your nesses administrator user account
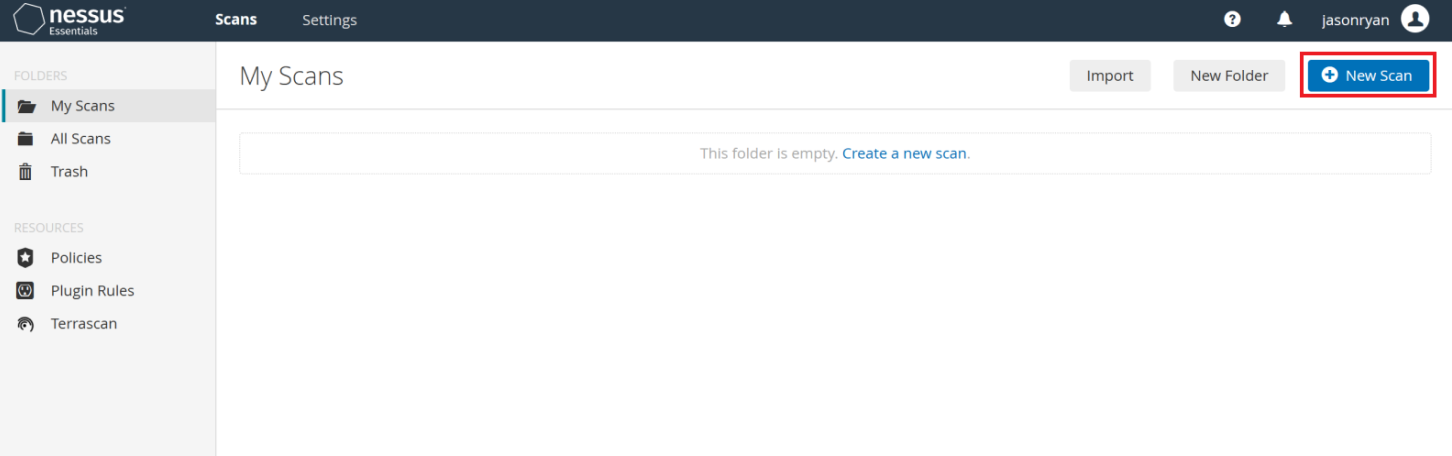
All work within Nessus with be through this web portal below:

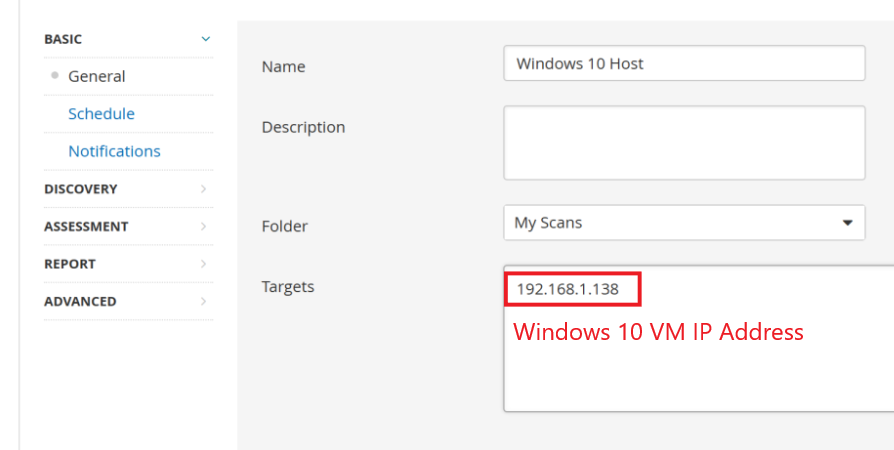
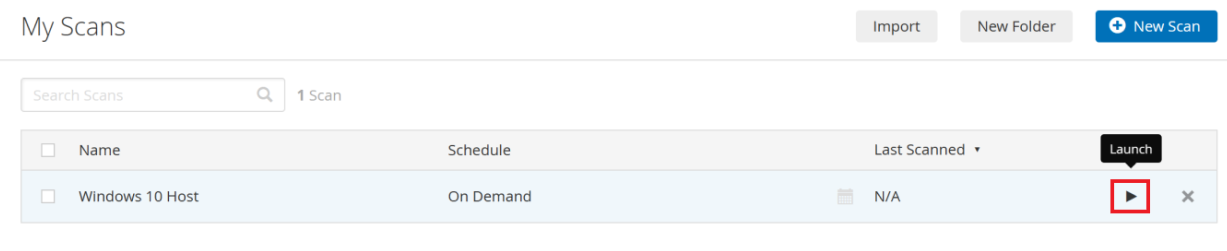
Our first scan against the Windows 10 victim machine will be a basic network scan. We have collected our victim client’s IP address via a ipconfig command on the machine and entered it as our Target IP when creating our basic network scan in Nessus. We will not be providing credentials to this scan thus I don’t expect us to get as much potential vulnerabilities detected than if we did provide credentials.
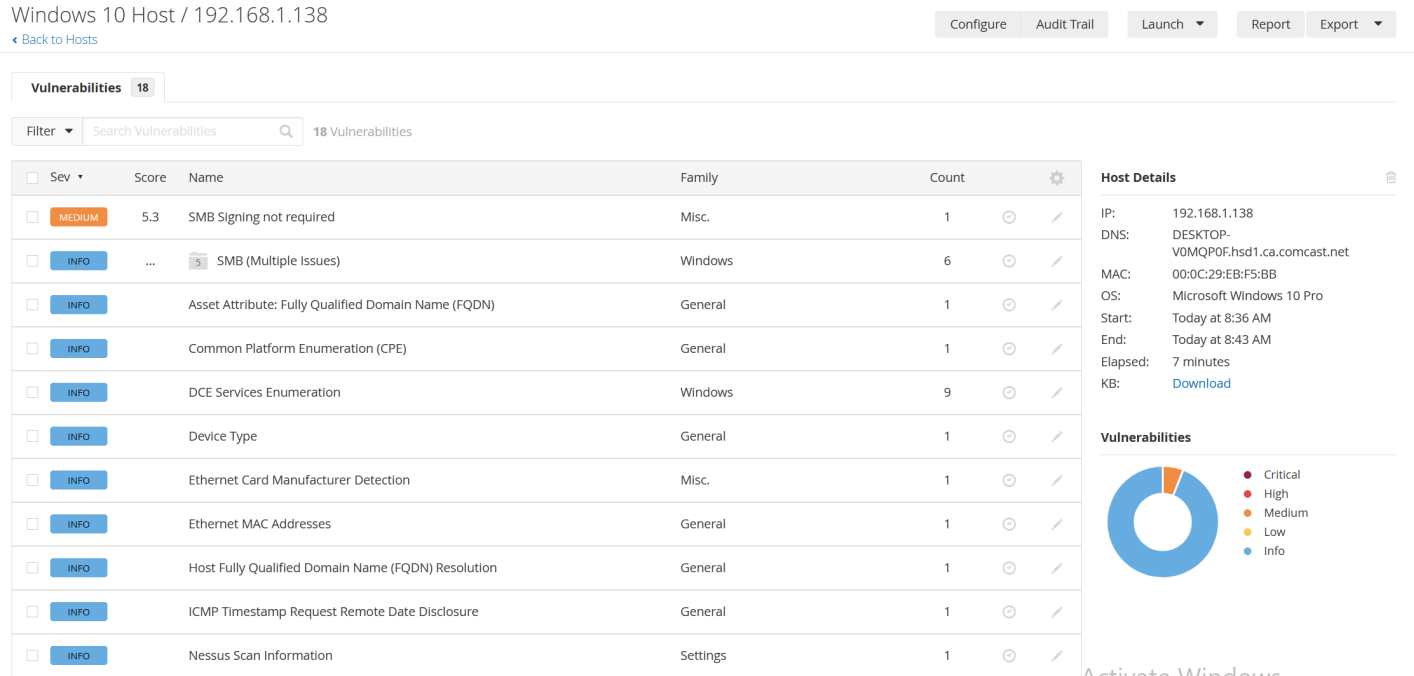
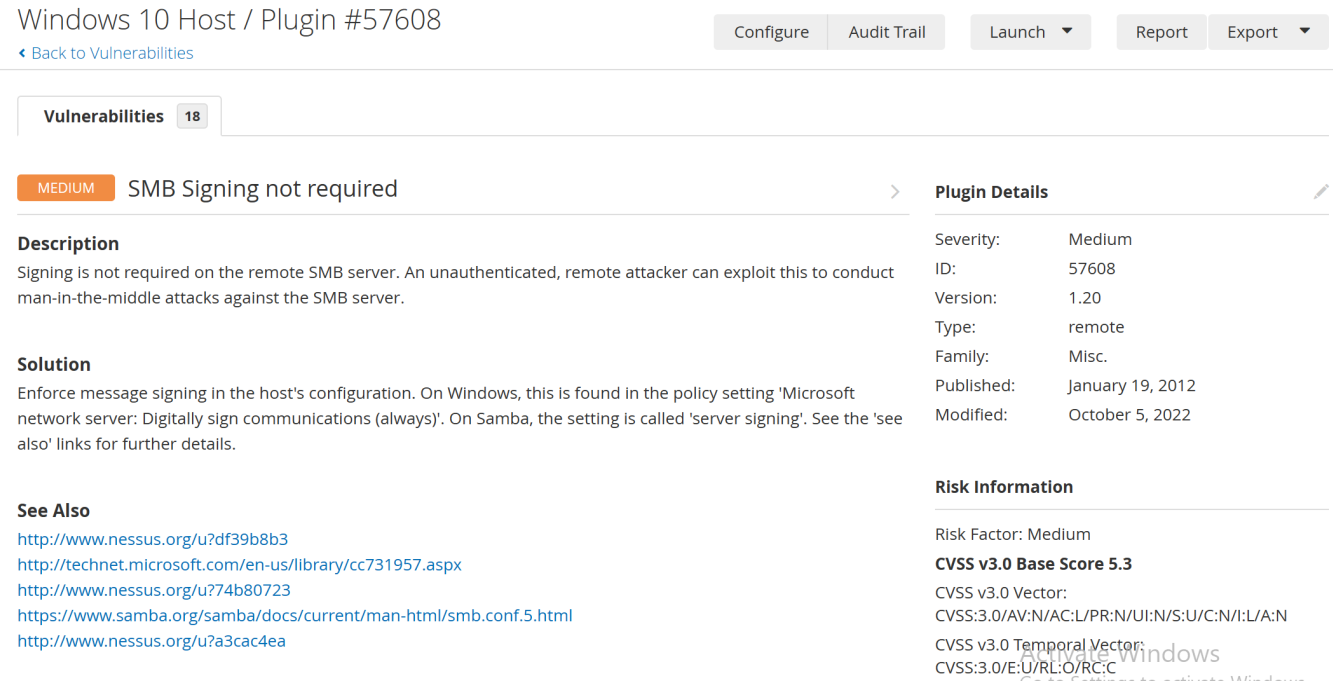
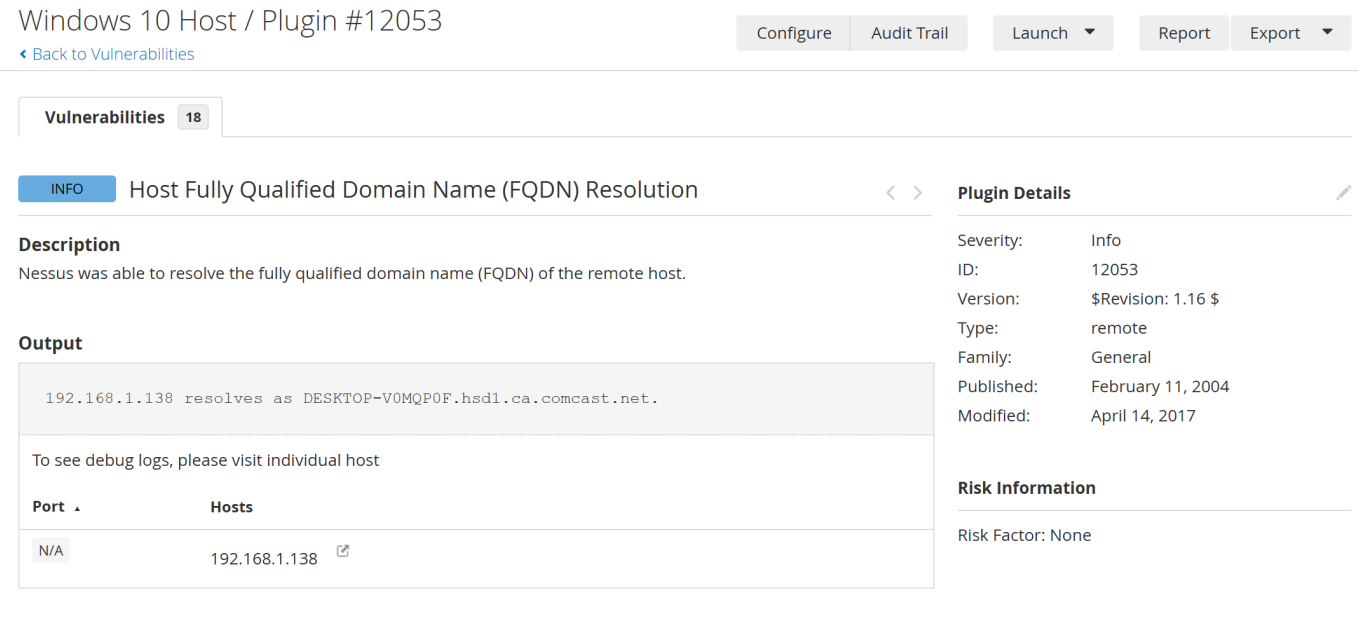
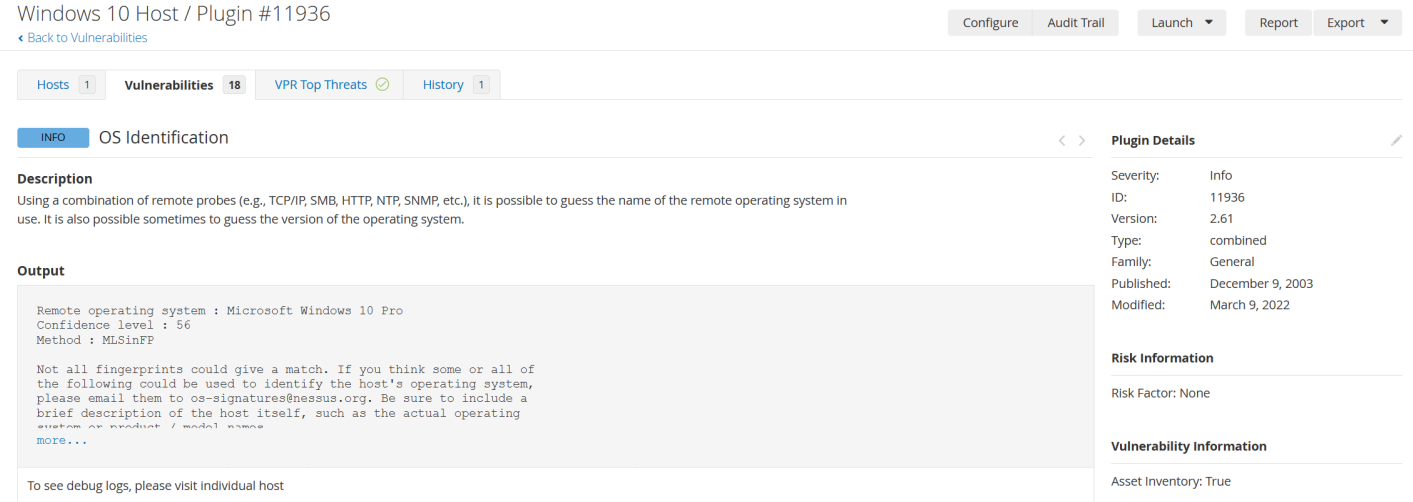
By running the basic network scan against the victim IP Address we were able to get lots of general information about the host such as its Operating System, ethernet MAC address, and FQDN resolution. Findings like these are sorted in the “Info” severity category as it is not an indication of a direct security risk but serves as a notice that this information was able to be discovered using this basic network scan.
For each detected vulnerability, Nessus provides a brief description of the vulnerability and a possible solution to remediate. Various support articles are also referenced for additional information.
Our second scan will be our same basic network scan however this time we are going to add a set of windows credentials to the scan. Adding credentials will allow us to uncover more about the possible vulnerabilities on the system as more can be discovered with additional access to the system.
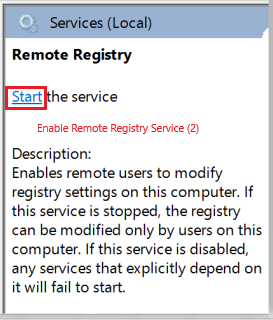
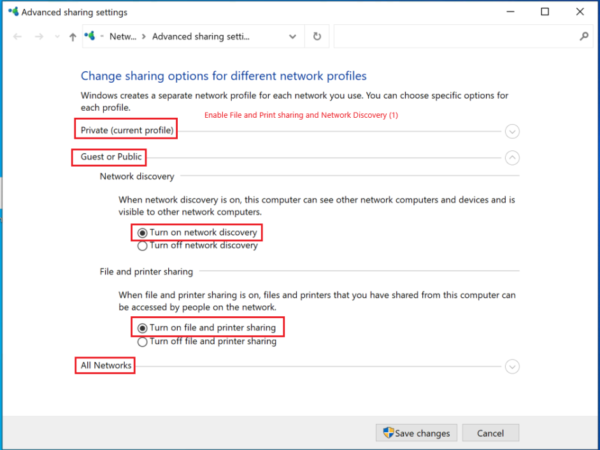
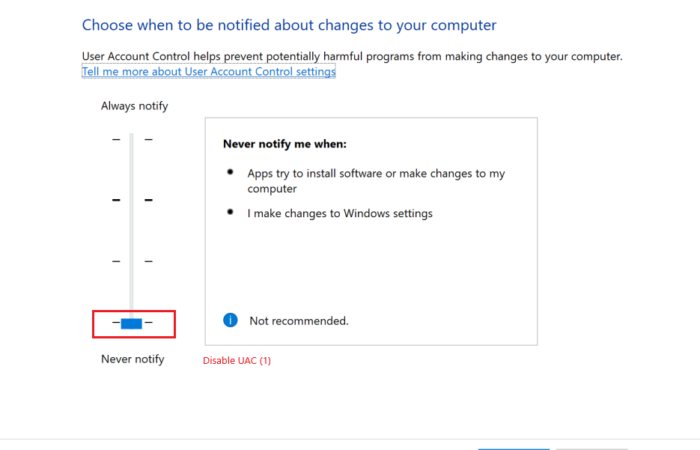
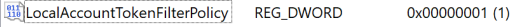
To allow our host VM to allow credentialed scan we first need to conduct the steps listed below:
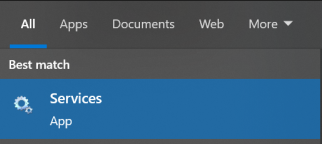
- Enable Remote Registry service
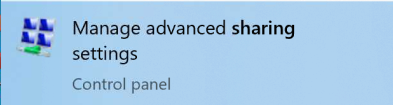
- Enable File and Printer Sharing and Network Discovery
- Disable User Account Control (UAC)
- Add “LocalAccountTokenFilterPolicy” DWORD in registry
Above are steps recommended by Nessus in order to do credentialed scans against windows hosts not on a domain.


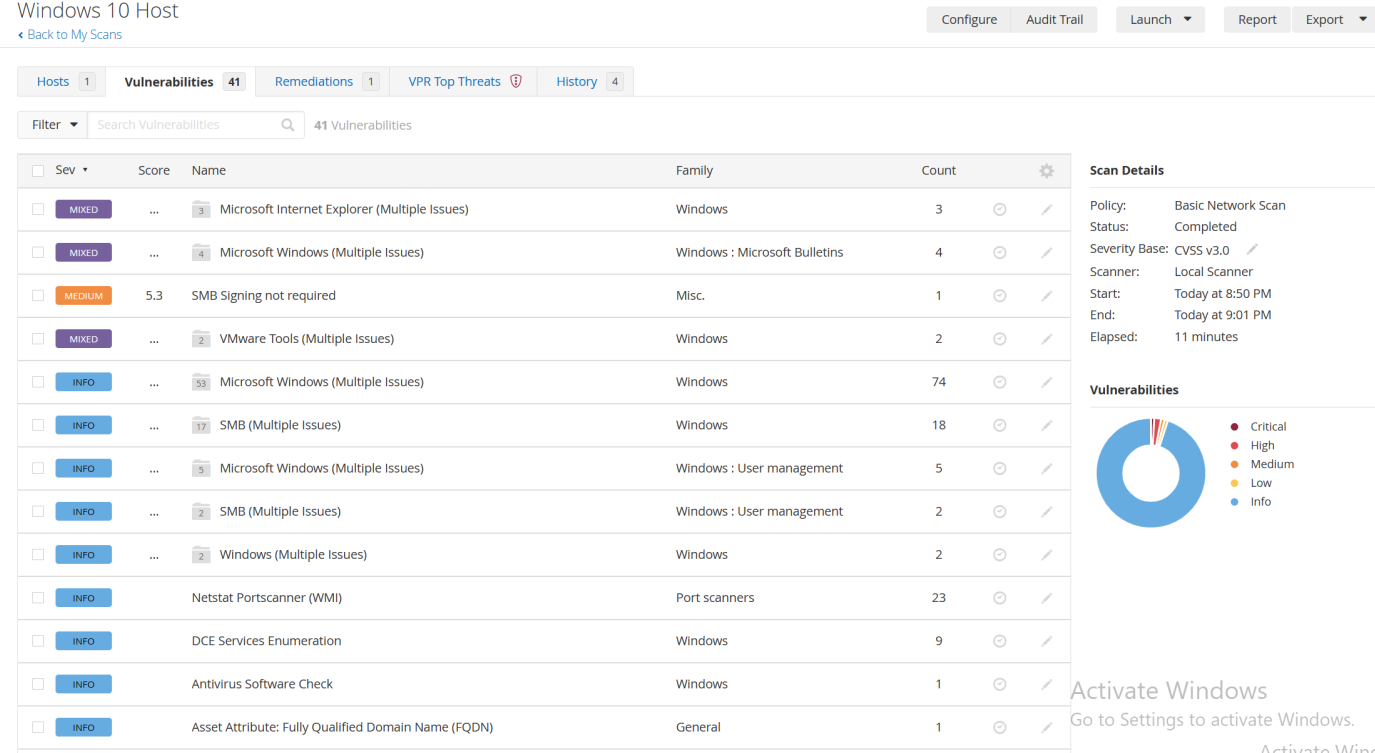
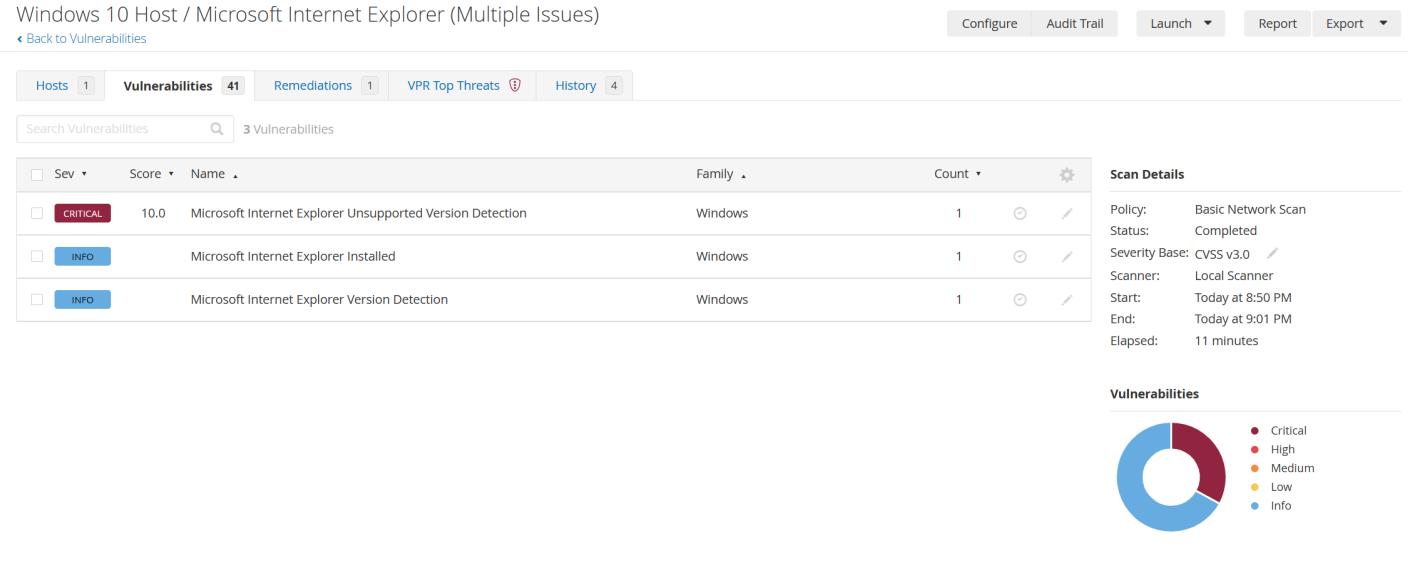
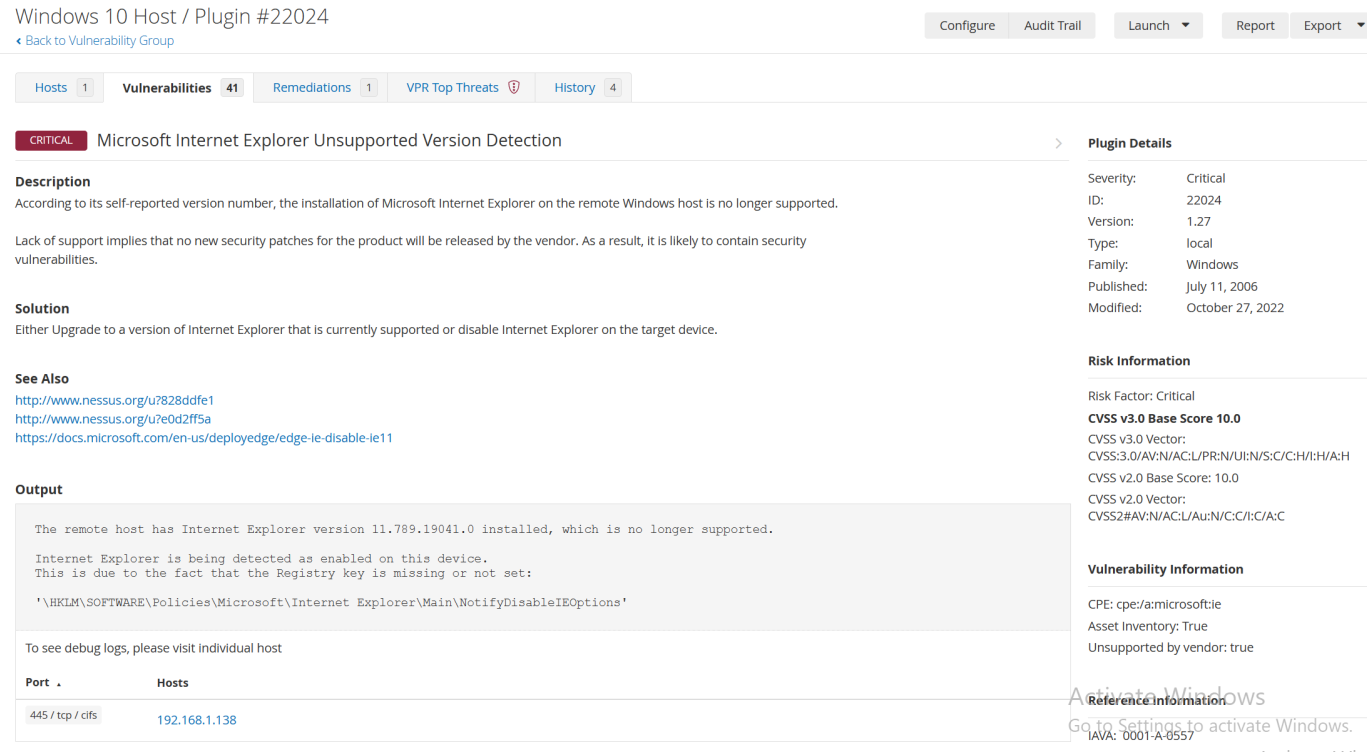
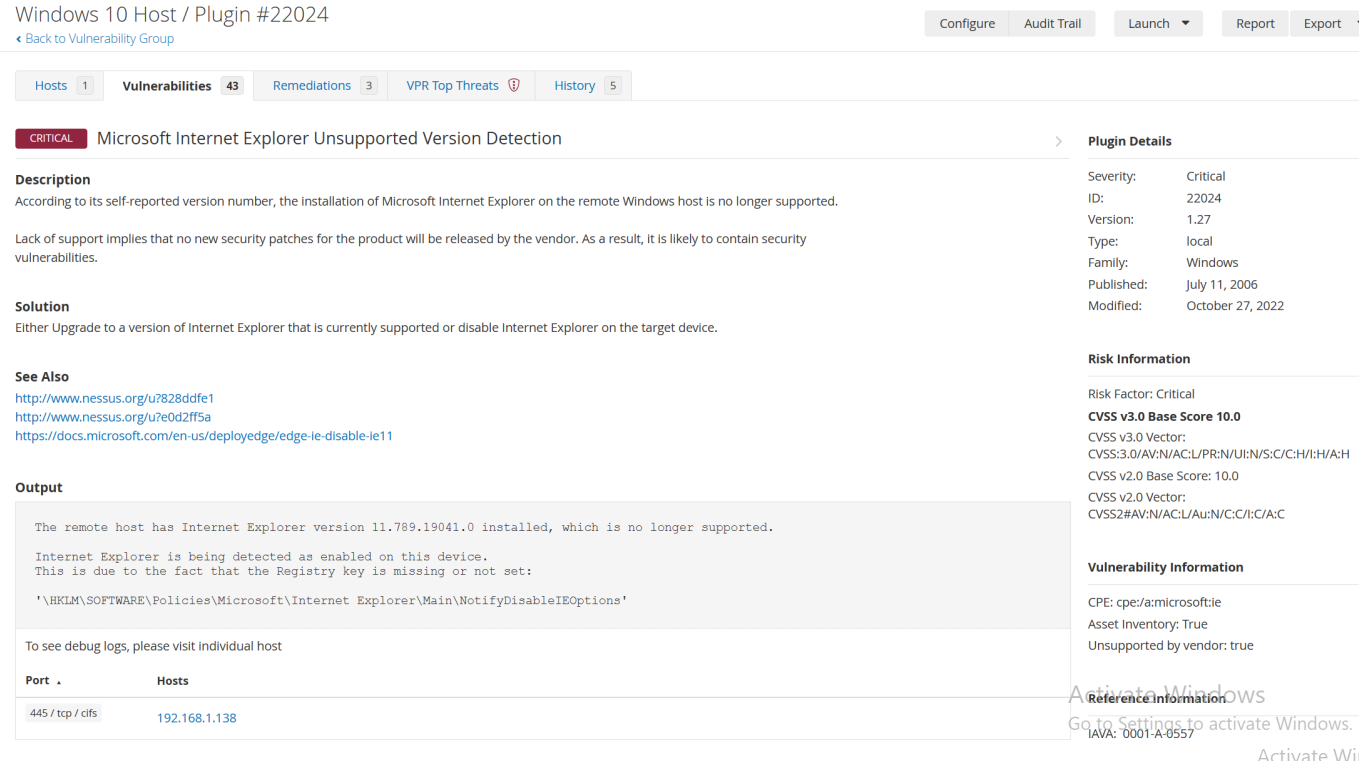
Adding credentials allows the scanner to run more deeply by being able to view file systems, registry and running services. The scanner was now able to pick up the missing security updates missing for this workstation as well as the unsupported Internet Explorer version.
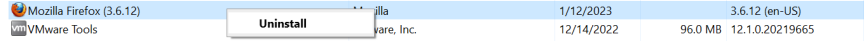
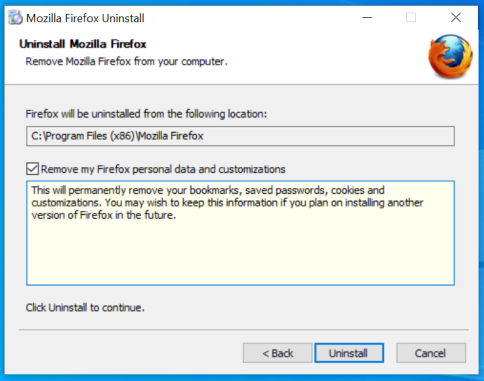
In our third scan, we will be installing a deprecated version of the Firefox web brower to see what the vulnerability scanner picks up

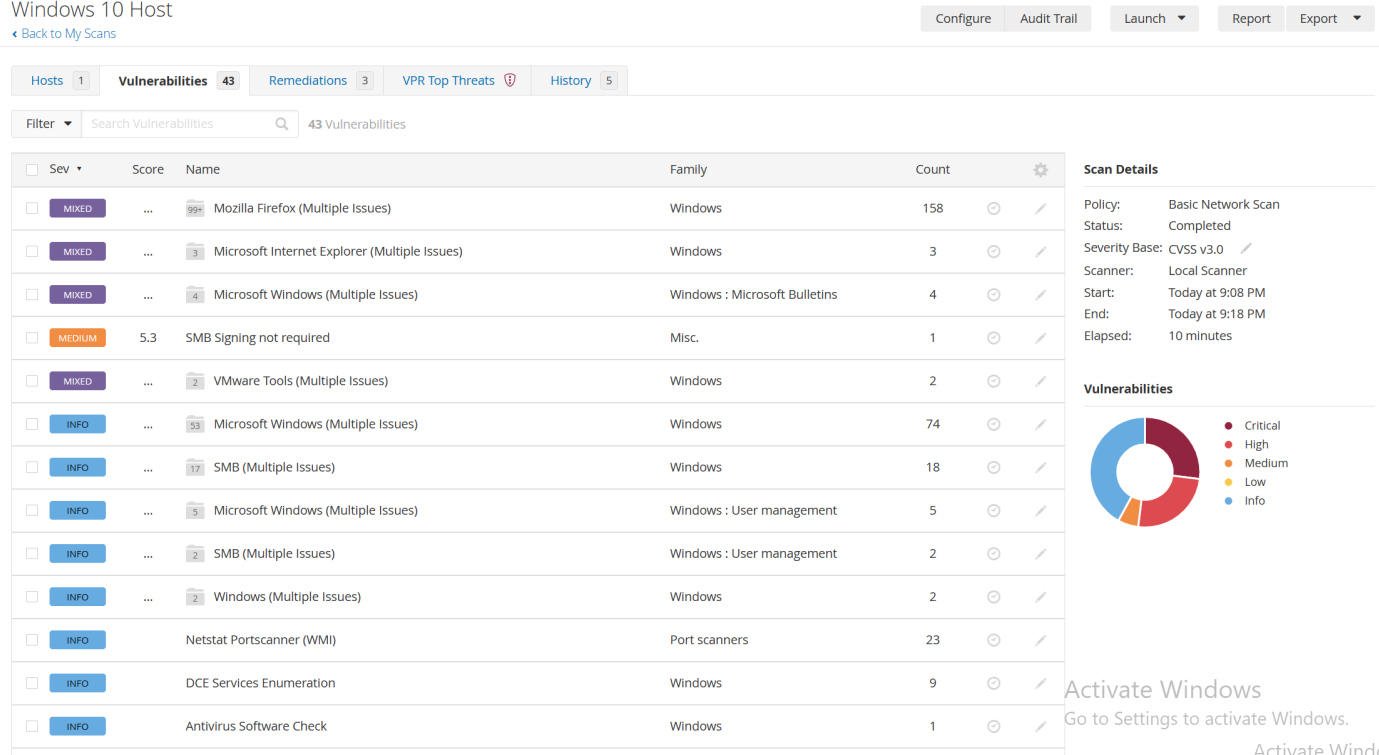
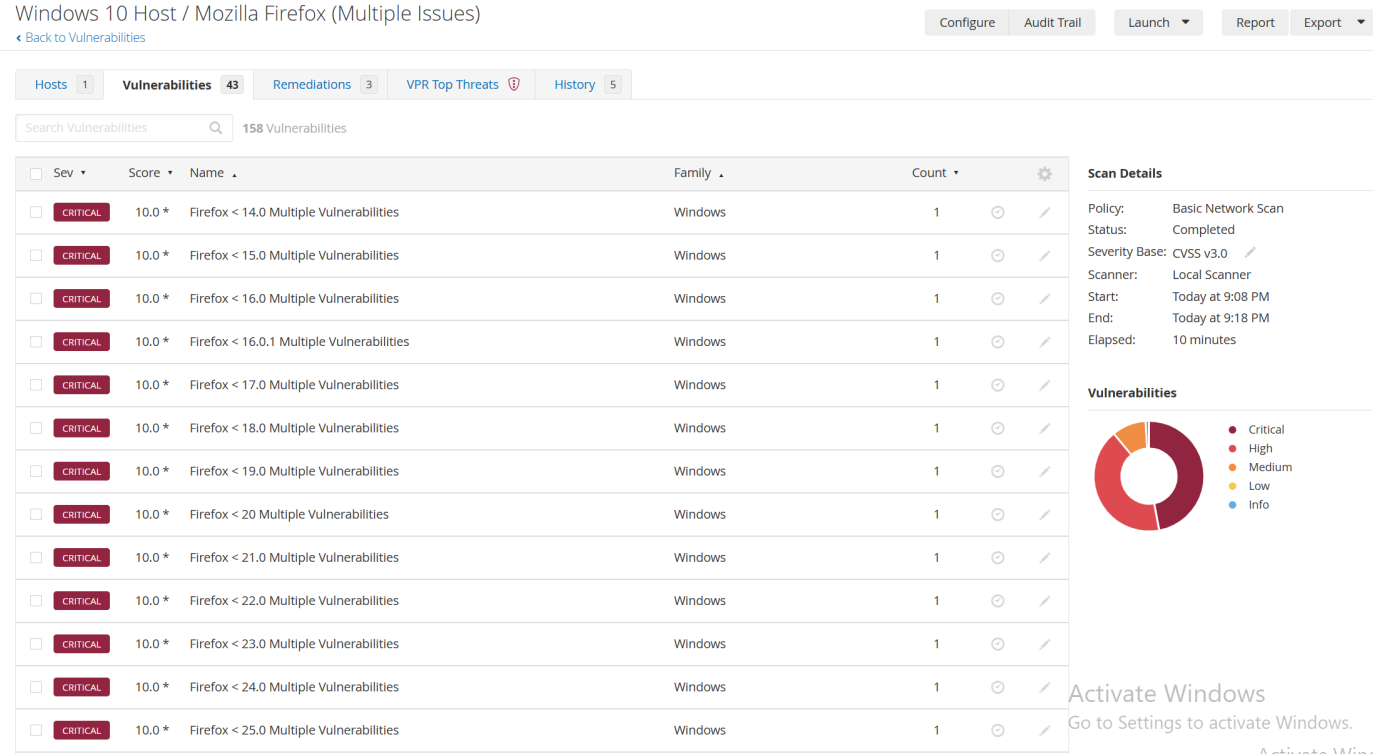
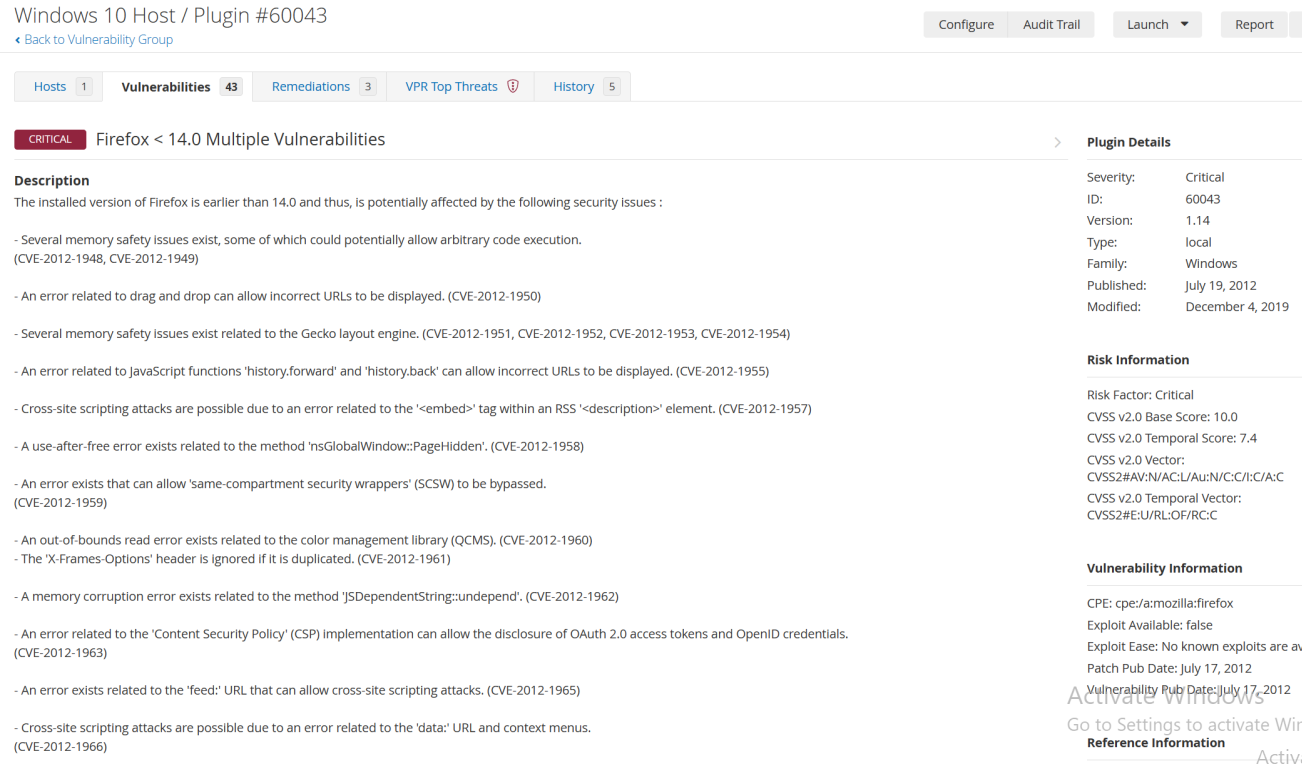
Every missed security update means an even larger attack surface for potential bad actors. This version of Firefox was released back in October 27th 2010. Our Nessus scan was able to pick up more than 158 instances of updates that patched critical vulnerabilities.
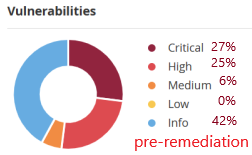
For our remediation phase we will be targeting the following high priority vulnerabilities detected from our scans:
- WinVerifyTrust Signature Validation Vulnerability
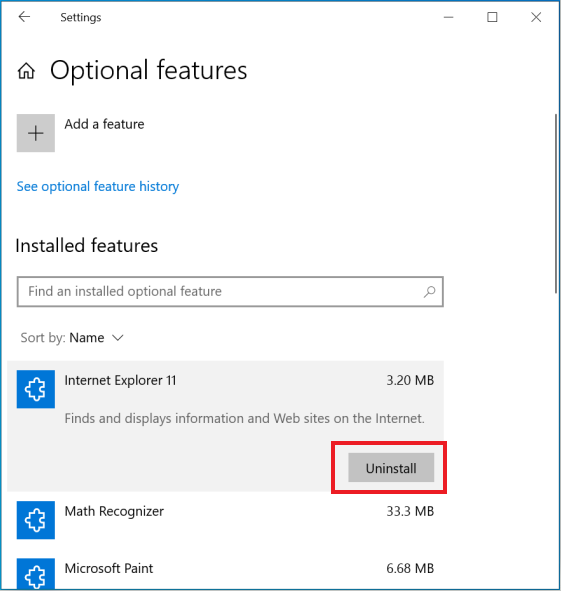
- Microsoft Internet Explorer Unsupported Version Detection
- Missing Security Updates
- Mozilla Firefox (Multiple Issues)
WinVerifyTrust Signature Validation Vulnerability
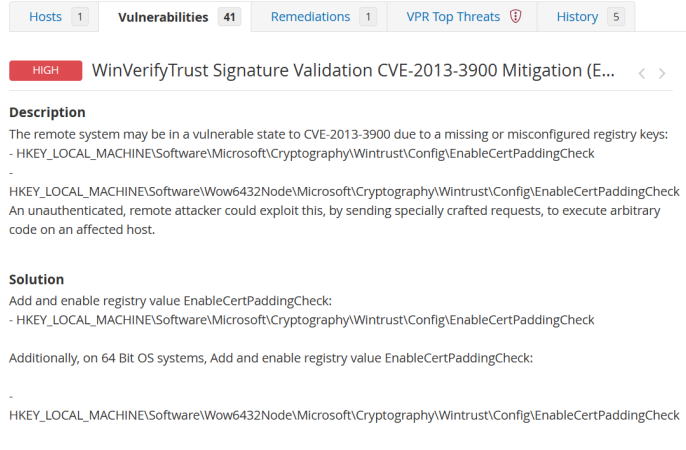
Our scans have detected that a remote code execution vulnerability that Microsoft mentions “exist with how the WinVerifyTrust function handles Windows Authenticode signature verification for portable executable (PE) files”
Microsoft explains that “An anonymous attacker could exploit the vulnerability by modifying an existing signed executable file to leverage unverified portions of the file in such a way as to add malicious code to the file without invalidating the signature”
More information about the vulnerability can be found linked on Microsoft’s Security Response Center website here.
- Per Microsoft’s recommendation, we will be remediating this vulnerability by enabling Authenticode signature verification improvements by modifying the registry of our target machine to add the EnableCertPaddingCheck value. Below we have created a .reg file to make the appropriate changes to the registry.
Missing Security Updates
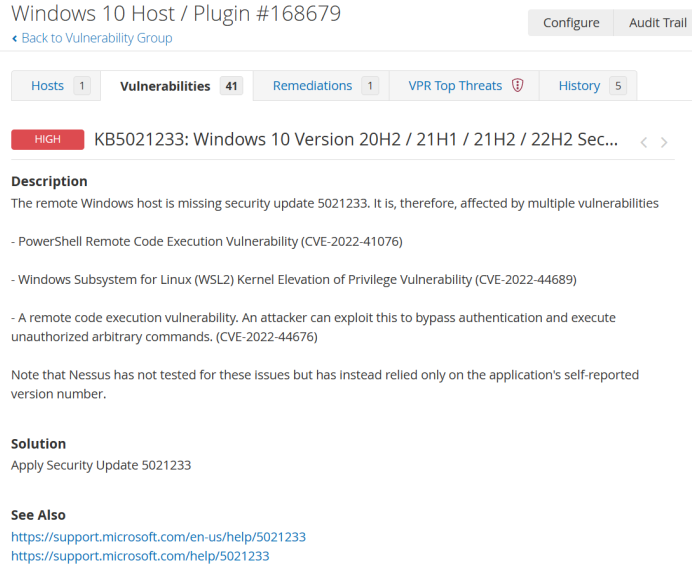
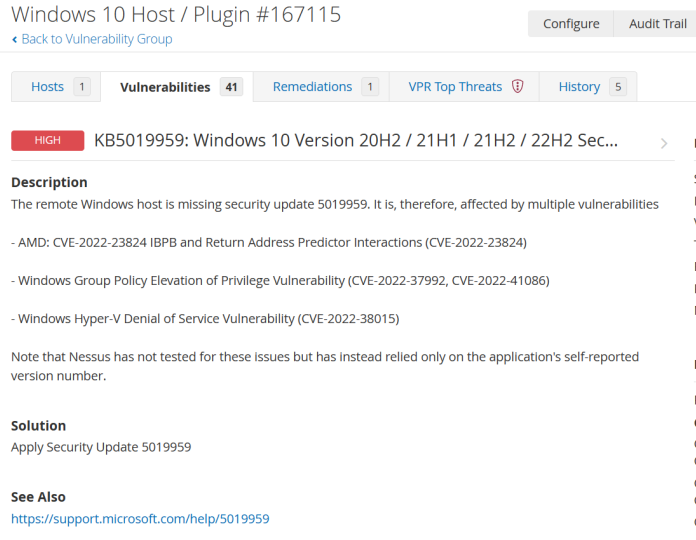
Simply put, security updates patch vulnerabilities. As the windows security update 5021233 and 5019959 is missing from this host, the host is exposed to:
- PowerShell Remote Code Execution Vulnerability (CVE-2022-41076)
- Windows Subsystem for Linux (WSL2) Kernel Elevation of Privilege Vulnerability (CVE-2022-44689)
- A remote code execution vulnerability. An attacker can exploit this to bypass authentication and execute unauthorized arbitrary commands. (CVE-2022-44676)
- AMD: CVE-2022-23824 IBPB and Return Address Predictor Interactions (CVE-2022-23824)
- Windows Group Policy Elevation of Privilege Vulnerability (CVE-2022-37992, CVE-2022-41086)
- Windows Hyper-V Denial of Service Vulnerability (CVE-2022-38015)
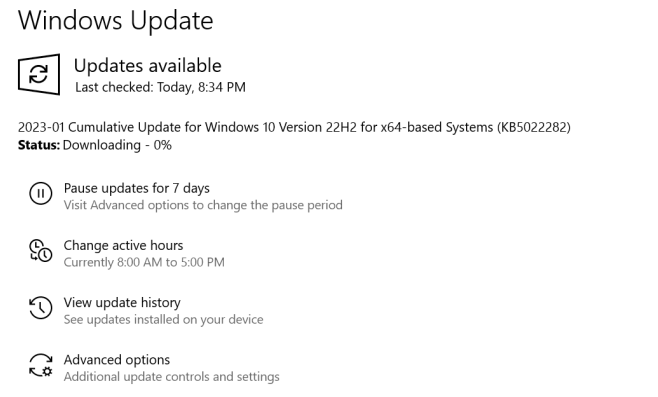
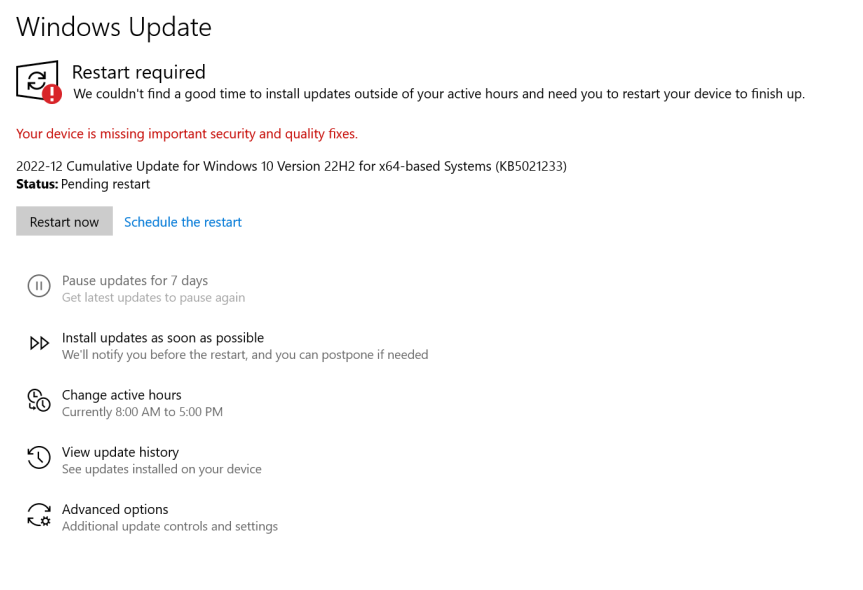
- To remediate these vulnerabilities we will be performing the all necessary updates via windows update within the settings.
Mozilla Firefox (Multiple Issues)
- To remediate this vulnerability, we will simply be uninstalling the deprecated application via control panel.
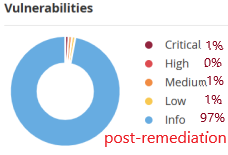
Nessus Essentials is a vulnerability scanner that we used in this lab to discover and assess vulnerabilities that were present on our Windows 10 target machine.
Nessus provided solution steps that we have followed to remedy each high priority vulnerability.
Once completed, we verified remediation by conducting a post-remediation scan and saw that the detected vulnerabilities from the Critical, high, or medium category had dropped to 3% of total vulnerabilities from 58%.
